Introduction
In the healthcare sector, the secure and efficient exchange of medical imaging data is crucial for diagnosis, treatment planning, and patient care. Digital Imaging and Communications in Medicine (DICOM) is the standard format for the communication and management of medical imaging information and related data. However, with the increasing threats to data security, ensuring the security and confidentiality of medical images transmitted over networks has never been more important.
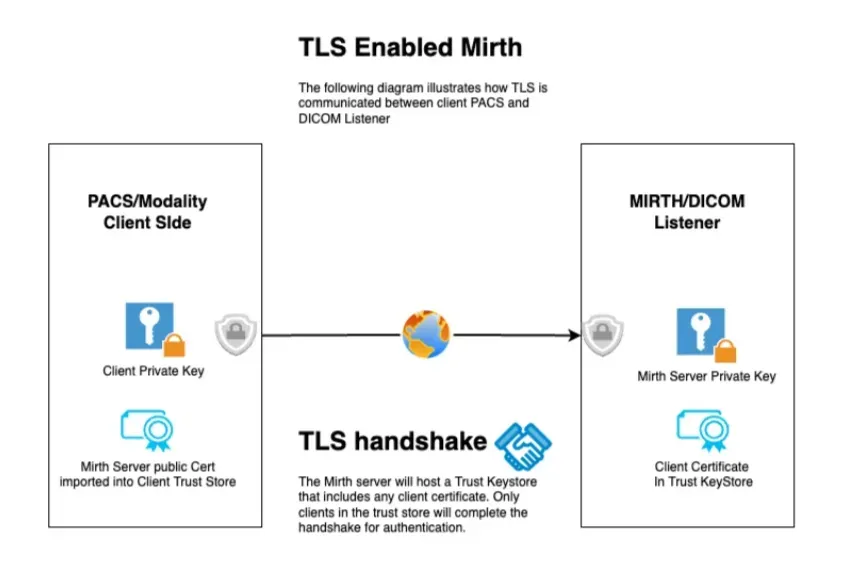
This guide provides a comprehensive overview of how to securely transmit DICOM files over Transport Layer Security (TLS) using the open source or commercial version of Mirth Connect, ensuring that sensitive patient data is protected against unauthorized access and cyber threats.
Setting Up Mirth Connect for DICOM over TLS
Getting Started
- Download KeyStore Explorer https://keystore-explorer.org/. The commands in this guide are tailored to KeyStore explorer but can easily be swapped out for similar java tooling.
- Download Mirth Channel
Video Tutorial
Generate and Import Certificates
To establish a TLS connection, you need a digital certificate from a trusted Certificate Authority (CA). This certificate can be self-signed but in some circumstances a certificate from a recognized CA is recommended.
- Generate Server Keys
keytool -genkey -alias MirthServer_PK -keyalg RSA -keystore MirthServer_PK.pfx -storetype PKCS12 -storepass 123456keytool -genkey -alias MirthServer_TS -keyalg RSA -keystore MirthServer_TS.pfx -storetype PKCS12 -storepass 123456
- Generate Client Keys
keytool -genkey -alias client_PK -keyalg RSA -keystore client_PK.pfx -storetype PKCS12 -storepass 123456keytool -genkey -alias client_TS -keyalg RSA -keystore client_TS.pfx -storetype PKCS12 -storepass 123456
- Export Certificate and import into Trust Store
keytool -keystore client_PK.pfx -storetype pkcs12 -exportcert -file Client_Cert.crt -rfc -alias Client_Cert_Aliaskeytool -import -trustcacerts -keystore mirthtlsKey_ts_trust.pfx -alias cl_pubdcm4chee -file Client_Cert.crt
Configure a Mirth Connect DICOM channel to use TLS
- In our channel settings, select AES and set client auth to no
- Add the path to the Keystore example: /opt/connect/appdata/keysandcerts/mirthtlsKey.pfx
- Add the path to the Trust Store example: /opt/connect/appdata/keysandcerts/mirthtlsKey_ts_trust.pfx
Test the new DICOM over TLS Connection
Test the transmission of DICOM files between the sender and receiver channels to ensure that the setup is working correctly. Use Mirth Connect’s message logging and error tracking features to troubleshoot any issues.
Best Practices and Considerations
- Keep your TLS certificates up to date to avoid disruptions in service.
- Regularly monitor and audit your DICOM transmissions to ensure compliance with healthcare regulations such as HIPAA.
- While TLS encrypts the data in transit, ensure your network is also secured through firewalls, intrusion detection systems, and other security measures.
Conclusion
Securing DICOM transmissions is essential in today’s digital healthcare environment. By leveraging Mirth Connect and TLS, healthcare organizations can protect sensitive patient data during transmission. This guide serves as a starting point for IT professionals in healthcare to implement secure, compliant, and efficient DICOM data exchange workflows. As healthcare technology evolves, staying informed and adapting to new security standards will continue to be paramount in protecting patient information and maintaining trust in healthcare systems.
Have questions or need help working with DICOM or Mirth Connect? Saga IT can help.
Learn more about Saga IT’s Mirth Connect consulting services Learn more about our Medical Imaging Integration services

